You’ve heard grand claims about blockchain: unhackable ledgers, instant decentralization, zero intermediaries, limitless scale. This guide cuts through the noise by tackling the most common blockchain myths and replacing them with plain-language facts, practical guardrails, and realistic examples you can use to make decisions. A quick note: blockchain choices often touch money, identity, and compliance. Treat this as educational guidance—not legal, financial, or security advice. Consult qualified professionals when decisions carry regulatory or financial impact.
In one line: A blockchain is a tamper-evident, replicated ledger maintained by a network via consensus. It’s useful when multiple independent parties need a shared, auditable source of truth—and it has trade-offs that must be understood.
Skimmable steps to sanity-check a blockchain claim
- Identify the exact problem (multi-party trust, audit, or automation?).
- Confirm the ledger type (public vs permissioned) and the consensus (PoW, PoS, etc.).
- Map the off-chain dependencies (oracles, key custody, governance).
- Run “numbers & guardrails” (throughput, fees, failure modes, legal fit).
- Choose minimal scope: put only what must be on-chain, move the rest off-chain.
1. “Blockchain equals Bitcoin (or ‘crypto’).”
Blockchain is the data structure and consensus method; cryptocurrencies are a prominent use case that live on top of certain blockchains. Many ledgers exist without a public token and are operated by known entities in a consortium (a “permissioned” model). NIST describes blockchains as tamper-evident ledgers replicated across participants with consensus rules—nothing in that definition requires a public coin. This distinction matters: if your goal is intercompany reconciliation or provenance, you may not need a tradeable token at all; if you’re designing an open, censorship-resistant marketplace, you probably do. Keeping the concepts separate lets you choose fit-for-purpose architectures, licensing, and security responsibilities rather than adopting coin-driven assumptions by default.
Why it matters
- Conflating blockchains with coins can bias decisions toward token-centric designs when a permissioned ledger would suffice.
- Regulatory scope, key management, and data handling differ dramatically across public and private networks.
- Clear separation helps explain cost models to stakeholders.
How to do it
- Start with the trust map: who are the writers, readers, and auditors?
- Decide if you need open participation (public) or gated membership (permissioned).
- Assess whether tokenized incentives actually solve a coordination problem—or add complexity. NIST Publications
Mini case (numbers)
A supply network with 5 companies each operating 2 nodes can run a permissioned ledger across 10 nodes, with on-chain hashes for proofs and off-chain documents in S3/IPFS. No token economics, simpler compliance, and predictable costs for storage and compute.
Synthesis: Separate technology (blockchain) from assets (crypto) so you can right-size governance, performance, and compliance.
2. “Blockchains are unhackable and perfectly immutable.”
Blockchains are tamper-evident, not magically invulnerable. Reorganizations (reorgs) and majority attacks can rewrite recent history on some chains; smaller networks are more vulnerable to 51% attacks, which have occurred in practice (e.g., Ethereum Classic). Even on robust networks, finality takes time and depends on the consensus’s guarantees. NIST notes that blockchains can, in some circumstances, undergo attacks that change history—less likely on large, economically secure chains, but not impossible. Understanding confirmation depth and finality mechanisms is essential before treating a transaction as irreversible.
Common mistakes
- Treating “one confirmation” as final for high-value transfers.
- Assuming every chain has the same finality model.
- Ignoring client diversity and software bugs that can cause consensus splits.
Numbers & guardrails
- Operational rule of thumb: set confirmation thresholds by value and chain risk (e.g., 30+ confirmations on a PoW chain for large payments; shorter for PoS with explicit finality, but still not instant).
- Track reorg statistics and validator/miner concentration before setting policy.
Mini case
An exchange waits 60 minutes before crediting high-value deposits on a PoW chain, reducing double-spend risk from deep reorgs while balancing user experience.
Synthesis: Treat immutability as probabilistic and policy-driven, not absolute. Engineer for finality, not folklore.
3. “Blockchain replaces databases.”
Blockchains and databases solve different problems. Traditional databases excel at complex queries, mutable records, and centralized control; blockchains excel at multi-party audit trails, provenance, and tamper-evidence—often with slower writes and higher costs. Even NIST emphasizes that blockchains are not general-purpose storage; large data typically belongs off-chain with on-chain hashes or pointers. Vendor and practitioner guides echo that databases remain the better fit for high-velocity CRUD workloads and analytics.
Quick comparison table
| Criterion | Blockchain (public/permissioned) | Traditional Database |
|---|---|---|
| Trust model | Multi-party, shared control | Centralized admin |
| Data changes | Append-only, tamper-evident | Mutable by design |
| Write speed | Slower (consensus overhead) | Fast (ACID/replication) |
| Storage | Costly on-chain; use off-chain + hashes | Cheap, scalable storage |
| Best for | Shared audit logs, provenance, tokenization | Operational apps, analytics, large files |
Numbers & guardrails
- Storing 1 GB fully on-chain can cost orders of magnitude more than object storage; use on-chain hashes plus off-chain storage (e.g., IPFS, S3). Ethereum Research
Mini checklist
- Do you need multi-organization writes?
- Do writers distrust each other?
- Is an audit trail the primary requirement?
- Can most data live off-chain with verifiable hashes?
Synthesis: Use blockchains for integrity across parties, not as your primary database.
4. “Blockchain is anonymous and private by default.”
Most public blockchains are pseudonymous, not anonymous: addresses are visible, transactions are traceable, and real-world identities can be linked via exchanges or analytics. NIST and global AML bodies (FATF) make this explicit; regulators impose “Travel Rule” obligations on Virtual Asset Service Providers (VASPs), requiring originator/beneficiary information for transfers above certain thresholds. For personal data, UK’s ICO highlights that GDPR rights and roles still apply on DLT, raising complex questions about controllers, erasure, and data minimization. Privacy-enhancing cryptography like zero-knowledge proofs (ZKPs) can hide data while proving correctness, but adoption is contextual and doesn’t override compliance duties.
Region-specific notes
- AML/CTF: FATF guidance expects VASPs to identify customers and share originator/beneficiary data under the Travel Rule.
- Data protection: GDPR/UK GDPR applies when personal data is processed; immutable ledgers complicate rights like erasure—architect with off-chain storage and on-chain pointers. FATF
Mini case
A fintech uses a public chain but stores only hashed customer IDs on-chain, with personal data kept in an encrypted database under role-based access. The design supports audits without exposing PII on-chain.
Synthesis: Plan for pseudonymity, compliance, and selective disclosure from day one.
5. “Smart contracts are automatically legal contracts.”
Smart contracts are code that executes rules; whether they are legally binding depends on contract law (offer, acceptance, consideration, intent) and jurisdiction. England & Wales’ Law Commission has explicitly concluded that existing law can accommodate smart legal contracts, but parties still need clear terms, notice, and mechanisms for dispute resolution. In many contexts, the best practice is a hybrid: natural-language terms that reference and govern the on-chain code. Electronic signature laws (e.g., UETA/ESIGN in the U.S.) may support enforceability when the parties agree to transact electronically.
How to do it
- Pair the code with plain-language terms covering jurisdiction, remedies, and failures (oracle downtime, forks).
- Make assent explicit (e.g., clickwrap with clear notice), then bind the on-chain action to that assent.
- Keep upgrade paths and emergency stops governed by agreed procedures.
Numbers & guardrails
- For consumer contexts, require two explicit actions: (1) visible terms view, (2) confirm-and-sign before triggering any on-chain effects.
- Maintain versioned hashes of both the code and the legal text.
Mini case
A commercial derivatives pilot ties a short natural-language ISDA-style annex to a smart contract. Traders click-to-accept the annex, then execute swaps via on-chain code that references the annex hash, enabling enforceability and audit.
Synthesis: Code automates performance; law recognizes agreements. Make both work together.
6. “All blockchains waste massive amounts of energy.”
Energy use depends on consensus. Proof-of-Work (PoW) systems like Bitcoin deliberately consume significant electricity to secure the network; empirical trackers (e.g., Cambridge’s CBECI) estimate network demand and revise methods over time. Proof-of-Stake (PoS) systems reduce energy use by orders of magnitude because security rests on staked value, not hashing. When Ethereum shifted from PoW to PoS, reputable coverage and technical docs reported a ~99%+ reduction in energy needs. U.S. EIA has also analyzed crypto mining’s electricity share in national terms. The key is to separate PoW economics from PoS designs and avoid per-transaction energy myths, which are often misleading.
Numbers & guardrails
- Treat PoW energy consumption as a network-level property, not “per transaction.”
- For sustainability targets, prefer PoS or permissioned BFT-style consensus and measure data center impact like any other workload.
Mini case
A payments pilot moves from a public PoW testnet to a permissioned BFT ledger across 6 nodes in certified data centers, reducing projected energy per node by >90% versus GPU mining rigs, while meeting internal carbon policies.
Synthesis: Energy impact is a design choice. Pick consensus to match your sustainability goals.
7. “Decentralization is binary—either you have it or you don’t.”
Decentralization lives on a spectrum: validator concentration, client diversity, governance keys, token distribution, and operational dependencies all shape real control. BIS research describes a “decentralisation illusion”—even systems marketed as decentralized often rely on chokepoints like admin keys or governance committees. In practice, many networks trade some decentralization for throughput or simplicity. Your task is to make the trade-offs explicit and acceptable for the risk.
What to measure
- Validator/miner concentration: top entities’ share.
- Client diversity: no single software client dominating.
- Upgrade governance: multisig thresholds, on-chain voting participation.
- Infra dependence: centralized RPCs, single cloud region.
Mini case (numbers)
A DeFi protocol’s admin key sits in a 4-of-7 multisig held by contributors across 3 jurisdictions; upgrades require a 48-hour timelock. This setup is more decentralized than a 2-of-3 multisig in one country—but less decentralized than immutable code with no upgradability.
Synthesis: Define decentralization goals per risk domain (consensus, governance, infra) and measure them continuously.
8. “Blockchains eliminate intermediaries.”
On-chain automation shifts which intermediaries you rely on; it rarely eliminates them. The oracle problem—getting trustworthy real-world data on-chain—introduces new infrastructure like oracle networks and bridges. NIST notes that when blockchains interact with the real world, validating external facts becomes the core challenge; BIS has analyzed the implications for DeFi. Even custody, compliance, and key recovery are mediated by service providers. The practical question is not “no intermediaries,” but “which intermediaries do we trust and how are they governed?”
Tools/Examples
- Decentralized oracle networks, price feeds, proof-of-reserves.
- “Legal wrapper” contracts around smart contracts to handle disputes.
- Attestation frameworks for IoT and identity.
Numbers & guardrails
- For price-sensitive protocols, require redundant feeds from 3+ independent oracle sources with deviation checks and failover logic.
- For data import, track SLA and evidence (signatures, Merkle proofs).
Synthesis: Design for verifiable intermediaries rather than imagining none exist.
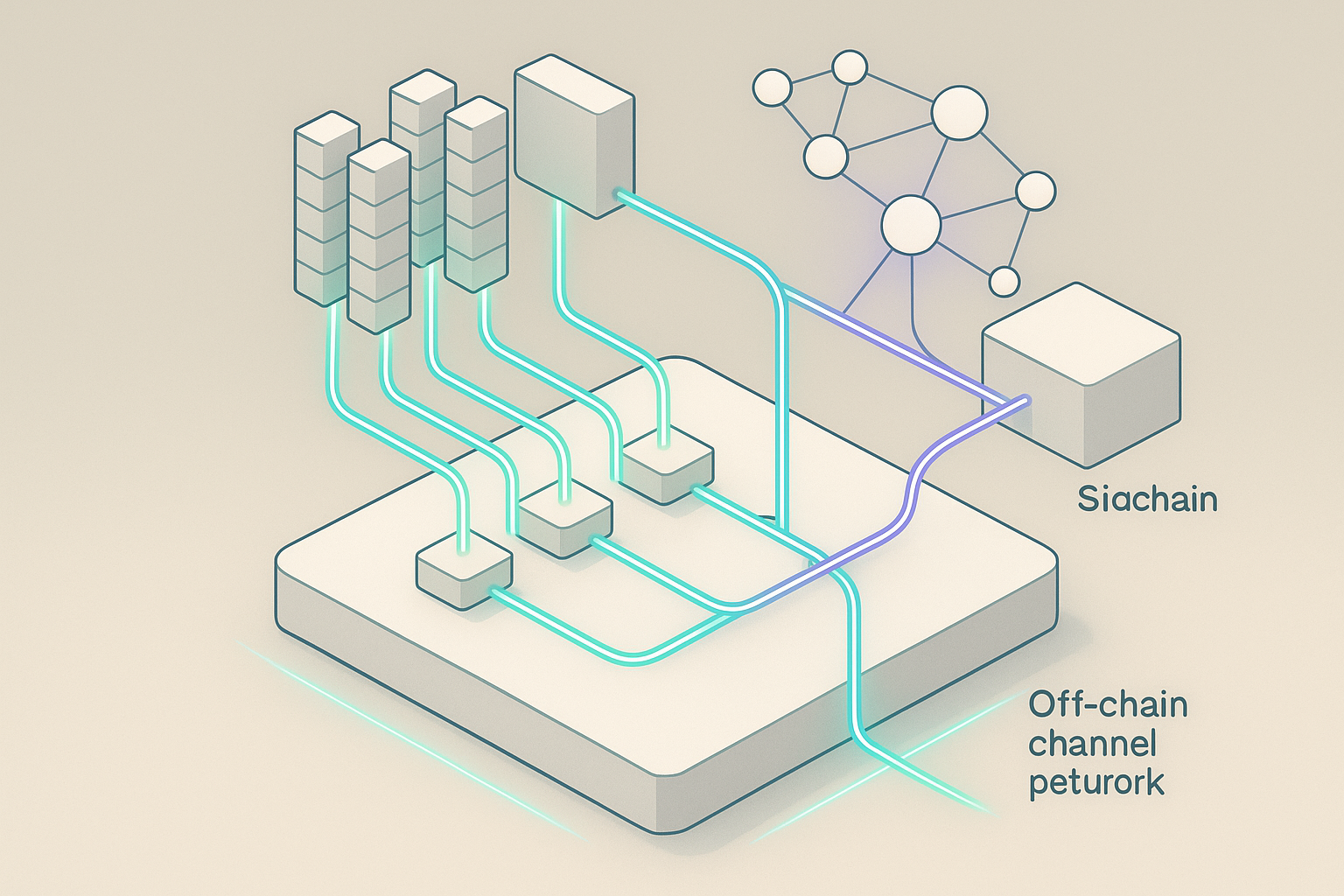
9. “Scalability is solved.”
Base-layer scalability remains constrained by decentralization and security trade-offs; newer capacity often comes from Layer 2 (L2) rollups that batch transactions and post proofs to the base chain. Authoritative ecosystem docs explain that rollups (optimistic and zero-knowledge) now dominate Ethereum’s scaling roadmap, but this introduces new trust and UX considerations (bridges, sequencers, data availability). BIS has also noted fragmentation pressures and trade-offs between capacity and centralization. Treat L2s as complements, not magic fixes.
Numbers & guardrails
- Expect thousands of TPS on L2 under favorable conditions, but plan for base-layer data availability limits and occasional congestion.
- For user funds, document exit assumptions and challenge periods; for ZK rollups, validate proving system assumptions.
Mini case
A ticketing app moves to a ZK-rollup, cutting median fees by >80% for peak events, while keeping settlement on mainnet for finality and dispute resolution.
Synthesis: Scale with L2s and batching—but budget for bridges, data availability, and operational complexity.
10. “Interoperability is easy—just use a bridge.”
Cross-chain bridges are among the riskiest components in Web3; they’ve been frequent targets of high-value exploits. Analytics and research reports catalog billions lost to bridge attacks and outline common failure modes (key compromise, faulty verification, replay). NIST also flags cross-chain risks in its stablecoin guidance. If you must bridge, choose designs with strong verification, minimize TVL exposed, and plan for incident response.
Mini checklist
- Prefer light-client or proof-based bridges over multisig custodial models.
- Cap exposure: shard liquidity; use circuit breakers and rate limits.
- Keep on-chain and off-chain monitors; rehearse freeze/recovery playbooks.
- Consider alternatives: native issuance, canonical bridges, or avoiding cross-chain where possible.
Mini case (numbers)
A game requires cross-chain items. The team caps any single bridge’s TVL at $10 million, enforces a daily mint limit, and uses two independent monitoring services, reducing worst-case loss and detection time.
Synthesis: Interop is a design program, not a checkbox. Treat bridges like high-risk critical infrastructure.
11. “Everything should go on-chain.”
Blockchains are poor fits for large, mutable, or private data. Best practice is to store minimal, integrity-critical references on-chain and keep bulk data off-chain in storage systems, anchoring with hashes. NIST’s guidance states that transactions should be relatively small and large data is “usually stored off chain,” with pointers or hashes recorded on-chain. This hybrid model satisfies auditability while controlling costs and supporting erasure/retention policies.
How to do it
- Put hashes (content IDs) and timestamps on-chain; store documents in IPFS/S3 with encryption.
- Use selective disclosure: present only proofs to verifiers.
- Rotate keys and apply data retention policies off-chain while keeping on-chain anchors stable.
Numeric example
A compliance archive writes a 32-byte hash per document to the chain (≈ <1 kB per record with metadata), cutting on-chain costs by >99.9% versus storing the files themselves, while preserving verifiable integrity.
Synthesis: Anchor the truth on-chain; keep the bulk where it’s safe, cheap, and compliant.
Conclusion
The loudest myths around blockchains come from treating them like silver bullets: unhackable, anonymous, costless, universal databases that remove intermediaries and scale forever. In reality, blockchains are credible tools for multi-party integrity with explicit trade-offs. Choose the ledger type that matches your trust map, keep most data off-chain with verifiable anchors, plan for oracles and governance, and scale through batching and L2s when appropriate. When you replace myths with measured engineering—finality thresholds, redundancy, emergency procedures, and legal wrappers—you get systems that auditors can trust and users actually enjoy. Your next step: write down your problem, list stakeholders, and test whether a minimal on-chain anchor plus off-chain systems solves it—then iterate.
Call to action: Share this guide with your team and use the checklists here to pressure-test your next blockchain proposal.
FAQs
1) What problems does blockchain solve better than a database?
Blockchains shine when multiple, independent organizations must write to the same record without a single administrator, and everyone needs a tamper-evident audit trail. They’re weaker at cheap storage, complex queries, and high-speed transactional processing. If your main need is a shared, verifiable log with clear provenance, a blockchain is worth testing; if you need analytics and frequent updates by one owner, a database is typically superior.
2) How “final” is a blockchain transaction?
Finality is probabilistic on many chains: deeper confirmations reduce the chance of reversal. Some PoS networks provide explicit finality after a protocol event; others rely on economic assumptions about reorg costs. For high-value transfers, set confirmation policies by chain and risk, and monitor reorgs in production. The Trail of Bits Blog
3) Are public blockchains compliant with privacy laws?
Compliance depends on what data you write. Public ledgers are transparent; writing personal data can create obligations that are hard to meet (e.g., erasure). The pragmatic pattern is to store only hashes on-chain and keep personal data off-chain under access controls, so rights and retention can be managed.
4) Do smart contracts need lawyers?
If you want enforceability and predictable outcomes, yes. Courts look for consent and clear terms. The safest approach is a hybrid: natural-language agreements that reference the code (via hash) and define governing law, dispute resolution, and upgrade procedures.
5) Is PoS always greener than PoW?
PoS generally uses far less energy because it replaces hashing with economic stake. That said, measure actual data center usage and workload mix. Don’t compare chains with per-transaction metrics; use network-level assessments and sustainability policies.
6) Can I avoid intermediaries entirely?
No. You’ll still rely on oracles, wallets, bridges, custodians, and governance processes. The goal is verifiable intermediaries with measurable SLAs and transparent security, not their total elimination. NIST Publications
7) Are L2 rollups as secure as L1?
They inherit security from the base chain for data availability and settlement but introduce new moving parts (sequencers, bridges, proof systems). Review the rollup’s design, operator set, and exit guarantees before treating it like L1.
8) How should I think about decentralization?
Track it across consensus, governance, and infrastructure. Look at validator concentration, client diversity, and upgrade controls. Document minimum thresholds you’re willing to accept and revisit them periodically. Bank for International Settlements
9) What’s the safest way to move assets across chains?
Prefer proof-based bridges and minimize value at risk with caps, rate limits, and rapid kill-switches. Consider whether you can avoid bridging by using native assets or a single settlement layer.
10) Does everything belong on-chain for audit?
No. Store proofs (hashes) on-chain and the bulk data off-chain with encryption and lifecycle controls. This gives you verifiability and privacy without runaway costs. NIST Computer Security Resource Center
References
- Blockchain Technology Overview (NISTIR 8202) — National Institute of Standards and Technology — 2018 — https://csrc.nist.gov/pubs/ir/8202/final
- Non-Fungible Token Security Considerations (NISTIR 8472) — National Institute of Standards and Technology — 2024 — https://nvlpubs.nist.gov/nistpubs/ir/2024/NIST.IR.8472.pdf
- Blockchain scalability and the fragmentation of crypto (BIS Bulletin No. 56) — Bank for International Settlements — 2022 — https://www.bis.org/publ/bisbull56.pdf
- Cambridge Blockchain Network Sustainability Index (CBECI) — Cambridge Centre for Alternative Finance — ongoing methodology page; major update article 2023 — https://ccaf.io/cbeci/ and https://www.jbs.cam.ac.uk/2023/bitcoin-electricity-consumption/
- Tracking electricity consumption from U.S. cryptocurrency mining — U.S. Energy Information Administration — 2024 — https://www.eia.gov/todayinenergy/detail.php
- Updated Guidance: A Risk-Based Approach to Virtual Assets and VASPs — Financial Action Task Force — 2021 — https://www.fatf-gafi.org/content/dam/fatf-gafi/guidance/Updated-Guidance-VA-VASP.pdf
- Distributed ledger technologies and data protection — UK Information Commissioner’s Office (ICO) — guidance hub — https://ico.org.uk/for-organisations/uk-gdpr-guidance-and-resources/data-sharing/distributed-ledger-technologies/
- Scaling — Rollups documentation — Ethereum.org — 2025 — https://ethereum.org/developers/docs/scaling/
- What’s the difference between a blockchain and a database? — IBM Think — reference article — https://www.ibm.com/think/topics/blockchain-vs-database
- Cross-chain bridge hacks — Chainalysis blog (multiple analyses) — 2022–2025 — https://www.chainalysis.com/blog/cross-chain-bridge-hacks-2022/ and https://www.chainalysis.com/blog/crypto-hacking-stolen-funds-2024/
- Stablecoin Technology and Security Considerations (NISTIR 8408) — National Institute of Standards and Technology — 2023 — https://nvlpubs.nist.gov/nistpubs/ir/2023/NIST.IR.8408.pdf
- Smart contracts: Law Commission advice — Law Commission of England and Wales — 2021 — https://lawcom.gov.uk/project/smart-contracts/