Smart contract fundamentals boil down to understanding what the contract is (a program with state on a blockchain), how it executes (deterministically with gas inside a virtual machine), and how it interacts with users and the outside world (transactions, interfaces, and oracles). A smart contract is a program deployed to a blockchain address with code and persistent state; it executes exactly as written when invoked by transactions. That’s the core definition.
Before we dive deeper, a quick roadmap: you’ll go from concept to production by (1) clarifying the on-chain problem, (2) choosing a network and language, (3) designing data and access control, (4) writing minimal contracts, (5) testing and fuzzing, (6) auditing and fixing, and (7) deploying, monitoring, and iterating. This guide unpacks each piece so you can reason clearly about design tradeoffs, costs, and security. Because smart contracts can hold value or enforce rights, treat them like safety-critical software and seek professional advice for legal or financial decisions.
1. What a Smart Contract Is (and Isn’t)
A smart contract is code plus state deployed to a blockchain address, executed by the network’s virtual machine; it’s not a human-readable legal document, though it can implement parts of a legal agreement’s logic. In practical terms, a contract exposes functions you or other contracts call via transactions; those calls can read or mutate state and emit events for off-chain consumers. This separation—code, state, events—is the conceptual skeleton you’ll use in every design. On widely used platforms, the definition is precise: a contract is “a collection of code (functions) and data (state) at a specific address,” and it runs deterministically on the network.
Why it matters
Understanding this definition keeps your scope laser-focused. If a feature needs external data that the blockchain can’t natively access (prices, weather, KYC), the contract can’t “just call the web.” You’ll need an oracle (covered later). If logic depends on randomness, you can’t rely on block.timestamp or miner-controlled values without risk; you’ll need verifiable randomness.
Common misconceptions
- “Code is law.” In many jurisdictions, code is evidence of intent, not law itself. Smart legal contracts may incorporate code and natural language together, and courts can interpret performance and disputes.
- “It’s just like a backend API.” It’s closer to a replicated state machine: every node re-executes your code, so nondeterminism and hidden I/O are not allowed.
Mini-checklist
- Define what must be on-chain versus off-chain.
- Identify state variables and events early.
- List external dependencies (data sources, tokens, other contracts).
In short: think “program with state under consensus,” not “server with a database.”
2. How Execution Works: Transactions, the VM, and Gas
Execution starts when a transaction targets a contract function (directly or via another contract). Nodes run your code inside the network’s virtual machine (e.g., the EVM), step by step, charging gas—a metering unit—for each operation. If you run out of gas, the state reverts. Fees are calculated as gas used × gas price, paid in the network’s native asset. Determinism is mandatory: identical inputs must yield identical results on every node, which is why contracts can’t make arbitrary web requests or read local clocks beyond limited block properties. This compute-for-gas model is specified in the protocol’s technical reference (“Yellow Paper”) and summarized in official docs.
Numbers & guardrails
- Back-of-envelope fee: if a call uses 120,000 gas at a 20 gwei gas price, the fee is 0.0024 native units (120,000 × 20e-9). Multiply by the asset’s market value to budget in fiat.
- Functions that write storage are costlier than pure reads. Emitting events writes to logs (cheaper than storage, still not free).
- Batch operations save overhead but risk hitting gas limits; split large loops or use pull-based patterns.
Common mistakes
- Unbounded loops over user-provided arrays can exceed block gas limits.
- Reverts on partial work can waste gas for callers; design idempotent, chunked workflows.
- Nondeterminism (e.g., block.timestamp for randomness) invites manipulation; use verifiable randomness.
Understand gas early, and you’ll design APIs and data structures that are both affordable and robust.
3. Data, Storage, and Events: Designing the Contract’s Memory
Contracts keep persistent variables in storage; function-local data lives in memory; call data parameters are read-only inputs passed with the call. Events are like append-only log entries that index topics for off-chain consumers (indexers, analytics, UIs) to react without bloating storage. The canonical docs explain the storage layout model and why you should prefer events for activity feeds and storage for business-critical state.
How to do it
- Model state: Separate critical balances/entitlements from ephemeral caches.
- Emit events for external subscribers (frontends, analytics). Don’t rely on events for on-chain logic.
- Choose mappings over arrays for sparse associations; keep arrays bounded if you must loop on-chain.
Compact table: data locations
| Location | Typical use | Notes |
|---|---|---|
| Storage | Balances, ownership, configuration | Persistent; costly writes; cheap reads relative to writes |
| Memory | Temporary computation | Volatile per-call; cheap; cannot persist |
| Calldata | Function inputs | Read-only; cheapest for external function params |
| Events | Activity logs for off-chain apps | Indexed; not readable by contracts |
Numbers & guardrails
- Optimize structs to pack into 256-bit slots where possible.
- Emit events for every state change users care about (transfer, role change, parameter update).
Finish each function by asking: “What state changed, and who else needs to know?” That keeps your contract observable and auditable without unnecessary storage bloat.
4. Interfaces and Standards: Tokens, NFTs, and Composability
Standards are the lingua franca of decentralized apps. Token interfaces (like fungible tokens and NFTs) define minimal functions and events so wallets, exchanges, games, and DeFi protocols can integrate without bespoke code. Good implementations are widely available in vetted libraries, preventing subtle bugs in allowance math, safe transfers, and hooks. Adhering to standards makes your contract “composable,” meaning other apps can snap to it like Lego bricks. Official docs and libraries provide canonical, audited starting points.
Why it matters
- Interoperability: A wallet can display and transfer your token if it exposes standard interfaces.
- Security-by-default: Reusing community-vetted code (access control, pausing, permit) sidesteps many footguns.
- Ecosystem reach: Marketplaces and protocols list your asset automatically when it matches expected interfaces.
Tools/Examples
- OpenZeppelin Contracts: drop-in implementations for fungible and non-fungible tokens, access control, pausing, and more.
- Interfaces: define external-facing functions only; keep your internal modules decoupled.
Common mistakes
- Rolling your own token logic.
- Missing events or returning values that deviate from the interface.
- Unsafe transfer patterns in NFTs (not using safe transfers to smart contract receivers).
Standards aren’t busywork—they’re scaffolding for network effects.
5. Languages, Tooling, and Testing: From Idea to Working Code
Most EVM-based contracts are written in Solidity, a statically typed language designed for the EVM, with tooling that supports compilation, debugging, and deployment. A professional workflow also includes unit tests, property-based fuzzing, and coverage measurement. Favor frameworks that let you simulate chain state, impersonate accounts, and run forked tests against real network snapshots. The Solidity docs establish language semantics; vetted libraries add safe building blocks and generators (wizards).
How to do it
- Choose a framework that supports scripting, testing, and deployments (e.g., Hardhat, Foundry, Truffle).
- Adopt a library for primitives (ownable roles, pausable guards, safe math where relevant).
- Write tests first for critical flows (mint, transfer, withdraw, upgrade).
- Fuzz properties like “total supply never decreases except by burn,” “no user can withdraw more than deposit.”
Numbers & guardrails
- Aim for 80–95% coverage on core contracts, but weight by risk: 100% for custody logic, lower for view helpers.
- Run forked tests against mainnet-like snapshots to catch integration issues.
Common mistakes
- Not pinning compiler versions or library releases.
- Testing only happy paths, ignoring reverts and malicious callers.
- Skipping gas snapshots; regressions creep in unnoticed.
Treat your toolchain like a cockpit: clear readouts and rehearsed checklists prevent surprises later.
6. Oracles and External Data: Bringing the World On-Chain
Blockchains can’t natively fetch real-world data. Oracles bridge that gap by delivering verified data (prices, randomness, identity attestations) to contracts in a tamper-evident way. Patterns vary—from data feeds aggregated by decentralized networks, to request–response models, to verifiable randomness functions used for fair lotteries and randomized selections. Reputable oracle networks provide docs, tooling, and security notes for integrating feeds, OCR-based aggregation, and VRF.
How to do it
- Identify data needs precisely (pair, decimals, freshness threshold).
- Select a delivery model: push-based feeds for high-frequency prices; request–response for occasional updates; VRF for randomness.
- Set guardrails: stale price rejection, deviation thresholds, circuit breakers that pause sensitive functions.
Mini case
You need a price that updates at most 60 seconds old with ≤0.5% deviation. You configure your contract to reject updates older than 60 seconds, require two consecutive updates within the threshold to lift a pause, and log every acceptance/rejection. This enforces bounded risk during volatile periods while keeping gas predictable.
Common mistakes
- Assuming any price is fresh or correctly scaled.
- Not handling oracle downtime or outliers.
- Coupling to a single provider with no fallback.
Design for graceful degradation: your app should fail closed, not fail catastrophically.
7. Threat Modeling and Security Basics: Build for Adversarial Environments
Smart contracts live on adversarial networks where anyone can call your functions. Security begins with threat modeling: enumerate assets (funds, governance, rare NFTs), adversaries (insiders, MEV bots), and trust boundaries (oracles, multisigs, upgrade keys). Use known vulnerability taxonomies and verification standards to structure reviews and testing. Leading organizations maintain standards and top-10 lists for smart contract risks, offering checklists and controls you can integrate.
Common vulnerability classes
- Reentrancy: external calls re-entering state-changing functions before invariants hold.
- Access control flaws: missing or misconfigured role checks.
- Arithmetic/logic errors: overflow in older compilers, rounding, price scaling, unchecked return values.
- Denial of service: unbounded loops, griefing via storage bloat, pausing held hostage.
- Initialization bugs: forgotten constructor logic in proxies; uninitialized variables.
Numbers & guardrails
- Require two-step admin actions (proposal → timelocked execution).
- Use rate limits (per-block/per-day caps) on sensitive flows.
- Ensure 0 reentrancy paths in critical state updates via patterns (checks-effects-interactions) and guards.
Tools/Examples
- OWASP Smart Contract Security Verification Standard for structured controls and verification activities.
Security is not a phase; it’s a mindset threaded through design, code, tests, and operations.
8. Audits, Formal Methods, and Continuous Assurance
An external audit validates assumptions and hunts for logic bugs you missed. But audits are not silver bullets; they complement your own rigorous testing, property-based fuzzing, and—where justified—formal verification that mathematically proves key invariants. Treat findings as backlog items: fix, retest, and document. For mission-critical systems, use multiple auditors with staggered scopes and reward reports via bug bounties. Industry standards encourage defensive coding and formal methods as part of best practices, not just optional extras.
How to do it
- Pre-audit hardening: clean tests, freeze scope, write specs (“this must never happen…”).
- Select auditors by domain expertise (tokens, AMMs, auctions), not just name recognition.
- Verify invariants with symbolic execution or model checkers for core properties (e.g., “reserves ≥ liabilities”).
Numbers & guardrails
- Budget 2–6 weeks per substantial review cycle depending on scope and complexity.
- Maintain a public changelog mapping each fix to a specific finding ID for traceability.
- Offer bounties scaled to potential loss; require proofs-of-concept.
Common mistakes
- Shipping significant changes after the audit without re-review.
- Treating audit reports as marketing artifacts rather than engineering inputs.
- No ongoing monitoring; issues resurface post-deploy.
Make assurance continuous: pre-commit hooks, static analysis, canaries, and runtime monitors reduce mean time to detect and fix.
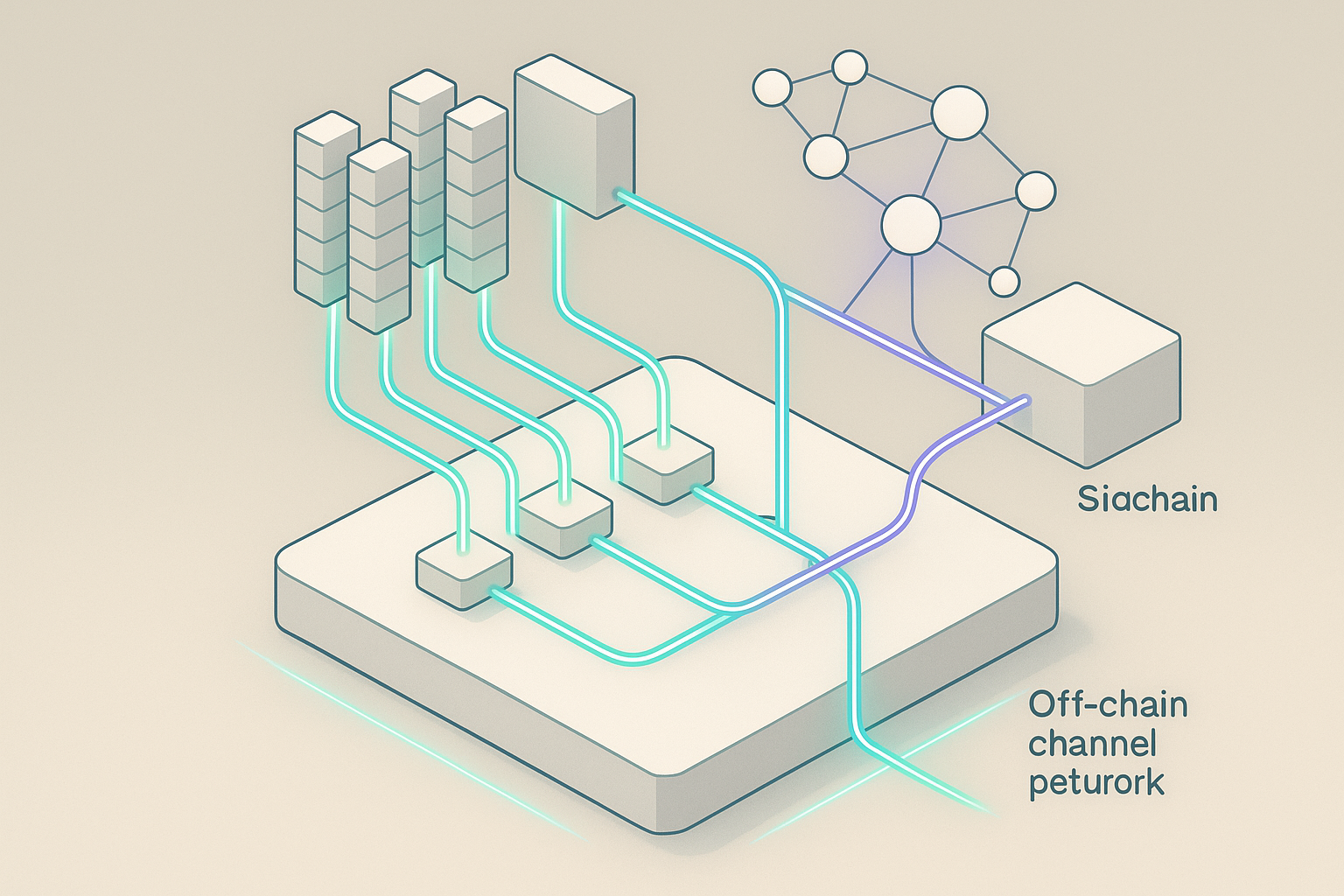
9. Fees, Performance, and Scalability: Designing for Constraints
Blockchains meter computation and storage. Your design should reflect that: write fewer storage slots, avoid unbounded loops, and batch operations judiciously. Gas fees vary by network conditions and function complexity; you control the gas used, not the gas price. For heavy apps, consider moving parts off-chain (proof systems, optimistic flows) or to rollups and sidechains while keeping settlement or critical logic on a base layer. The protocol spec explains why every operation has a cost and how limits protect the network.
Numbers & guardrails
- Fee math: a function using 75,000 gas at 15 gwei costs 0.001125 native units.
- Storage minimization: prefer packed structs and hashes; migrate archives off-chain.
- Batching: process N items per call with an upper bound to avoid exceeding block limits.
How to do it
- Profile gas regularly; fail CI on regressions.
- Use events for logs; store only what you must for correctness.
- Adopt L2s for high-throughput use cases; understand finality and bridging trust assumptions.
Common mistakes
- On-chain iteration over user lists.
- Duplicate storage of derivable values (e.g., counters you can recompute).
- No fee education for users; provide estimates in the UI.
Design like you’re paying per instruction—because you are.
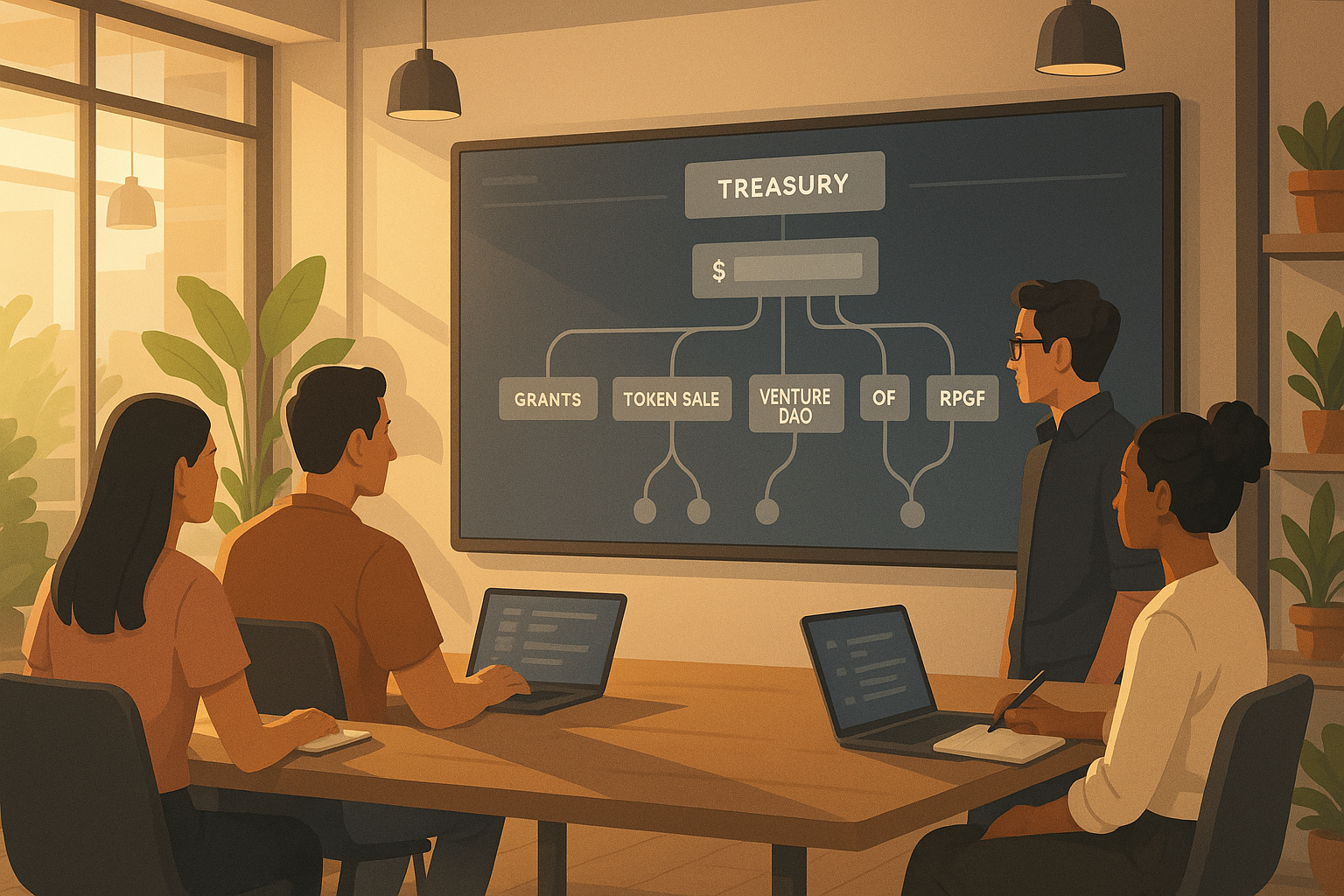
10. Upgradeability, Proxies, and Governance
Immutability is a feature, not a bug, but many systems need controlled evolution. Proxy patterns separate a contract’s storage (proxy) from its logic (implementation), letting you upgrade logic without migrating state. This introduces new risks: storage layout must remain compatible; admin keys become sensitive trust anchors; and governance processes must ensure upgrades are safe and transparent. Established libraries provide well-tested proxy implementations and upgrade helpers.
How to do it
- Decide governance early: multi-sig ownership, timelocks, or on-chain voting.
- Lock storage layout: reserve gaps for future variables; never reorder existing slots.
- Stage upgrades: deploy candidate logic → run tests on a fork → schedule via timelock → execute after review.
Numbers & guardrails
- Require M-of-N signers (e.g., 2-of-3 or 3-of-5) for upgrade actions.
- Use time delays (e.g., multiple days) so stakeholders can review changes.
- Maintain runbooks for rollback and pause.
Common mistakes
- Initializing the implementation contract (brick risk).
- Forgetting to restrict the upgrade function.
- Storage collisions from careless layout changes.
Upgradeability trades code finality for governance trust—be explicit about that trade and document it.
11. Smart Legal Contracts and Compliance Touchpoints
A smart legal contract blends natural-language obligations with code that performs some terms automatically. In many jurisdictions, existing contract law can accommodate these agreements without specific new statutes, as explained by law reform bodies. Still, enforcement, consumer protections, and jurisdictional questions require careful counsel. Your engineers should write code that clearly reflects agreed terms and exposes logs and administrative controls that support dispute resolution.
How to do it
- Map legal clauses to code: payment triggers, escrow release, termination conditions.
- Retain human oversight for exceptional cases via pausing or arbitration hooks.
- Ensure observability: events for all legally significant state changes.
Region notes
- England & Wales: official conclusions indicate the legal framework can support smart legal contracts; code can form part of an agreement. Consult counsel for sector-specific regulation.
Common mistakes
- Assuming unilateral code changes are always acceptable.
- No contingency plans for bugs in self-executing logic.
- Forgetting consumer rights or data protections when linking identities.
Treat code as part of the evidence chain: clarity and logging help everyone, especially in edge cases.
12. Operations: Deployment, Monitoring, and Incident Response
Shipping the contract is the beginning, not the end. Production-grade operations cover deterministic builds, verifiable deployments, on-chain monitoring, alerting, key management, and emergency procedures. Use reproducible builds and publish source code for verification so anyone can match bytecode. Set up monitors for critical events (mint, withdraw, role changes), error rates, and oracle freshness. Maintain playbooks for pausing contracts, rotating keys, and communicating incidents.
Mini-checklist
- Before deploy: freeze scope, tag releases, verify bytecode, publish ABIs, document parameters.
- After deploy: enable alerts, publish addresses, set multisig owners, run canary transactions.
- Emergency: test pausing, withdrawal limits, and admin rotations on a fork; document comms templates.
Numbers & guardrails
- Define an SLO (e.g., alerts within 5 minutes; critical fixes staged within 24 hours).
- Keep least-privilege roles: a deployer account that cannot touch funds; a separate, time-locked governor.
- Rotate keys on a predictable cadence; log custody and approvals.
Common mistakes
- Undocumented admin powers and unclear escalation.
- No monitoring for oracle staleness or upgrade events.
- Publishing addresses without source verification for explorers.
Ops converts “secure-by-design” into “secure-in-reality.” Plan for normal days and bad days alike.
Conclusion
You now have a practical map of smart contract fundamentals: what contracts are, how they execute within a virtual machine for gas, how to design state and events, and how standards, tooling, and oracles enable composable applications. You’ve also seen why security is an ever-present discipline, how audits and formal methods fit in, how upgradeability and governance trade immutability for flexibility, and where legal considerations enter the picture. Take the next step by drafting a minimal contract that expresses your business invariants, writing tests that prove them, and wiring continuous assurance and monitoring around the code. When each building block is intentional—design, verification, operations—you ship faster with fewer surprises and a safer user experience. Ready to apply this? Start by sketching your on-chain state, listing critical invariants, and picking one standard to implement this week.
FAQs
1) What is a smart contract in simple terms?
It’s a program on a blockchain that holds state and runs exactly as written when called by transactions. Think of it as a shared database table with embedded rules that everyone can verify. Functions read and write state, and events announce changes for off-chain apps. This determinism and transparency let strangers coordinate without a traditional central server.
2) How do smart contracts “know” about real-world prices or data?
On their own, they don’t. Contracts can’t fetch web APIs directly; they rely on oracles that deliver signed, verified data to the chain. You’ll choose push-based data feeds, request–response, or verifiable randomness depending on your use case, and add freshness and deviation checks to keep logic safe.
3) Why are gas fees necessary?
Gas meters computation and storage so the network can fairly allocate scarce resources and prevent abuse. Each opcode has a gas cost; a transaction’s fee equals gas used times gas price. If gas runs out, state changes revert to preserve consistency. Understanding this model helps you design affordable, reliable functions.
4) When should I use an upgradeable proxy?
Use proxies when the system must evolve under governance, but recognize the trust trade-offs. Keep storage layout stable, add timelocks and multi-signature approvals, and document procedures for upgrades and rollbacks. If your contract is simple and final, immutability with no upgrade path can reduce risk.
5) Are smart contracts legally enforceable agreements?
They can embody parts of agreements, and many legal systems can treat them within existing contract law. Often, natural language terms govern the relationship while code automates performance. Work with counsel to map clauses to code and plan for exceptions and dispute resolution.
6) What are the most common security pitfalls?
Reentrancy, missing access control, unbounded loops, logic and math errors, and unsafe external calls top the list. Follow a structured verification standard, adopt vetted libraries, write property-based tests, and bring in independent auditors. Keep monitoring and bug bounties active after deployment.
7) How do events differ from storage?
Storage persists data for contracts to read later; events record logs for off-chain consumers and are not intended for on-chain reads. Use storage for balances and rights; use events to inform UIs, indexers, and analytics of changes. Designing both together keeps the app consistent and observable.
8) Which language should I start with?
If you’re targeting EVM networks, Solidity is the dominant choice with mature tooling and community support, plus high-quality libraries for common patterns. Whatever you choose, pin versions, test extensively, and lean on proven components rather than reinventing primitives. docs.soliditylang.org
9) How do I estimate user fees before a transaction?
Estimate gas used by simulating the call (most libraries and wallets can do this), multiply by a proposed gas price, and show the user the total in native units and fiat. Provide ranges and warn that volatile conditions can change final costs. Avoid hiding fees in loops that may exceed limits.
10) Do I need an oracle for randomness?
For fair drawings, lotteries, or randomized game elements, yes—use verifiable randomness that proves the number wasn’t manipulated. Avoid relying on miner-influenced values like timestamps. Many oracle networks provide ready-made randomness products with on-chain proofs.
11) What belongs on-chain versus off-chain?
Put the minimum necessary for trust and settlement on-chain: balances, entitlements, and critical parameters. Move large data, heavy computation, and analytics off-chain, feeding results back through proofs or oracle updates. This balances transparency with performance and cost.
12) How do audits fit into the release plan?
Treat audits as part of a continuous assurance pipeline: pre-audit hardening, external review, fix-and-retest, source verification on deployment, runtime monitoring, and bug bounties. Avoid scope creep after the audit without a re-review, and keep a public mapping from findings to fixes for accountability.
References
- “Introduction to smart contracts,” Ethereum.org, publication page. ethereum.org
- “Introduction to Smart Contracts,” Solidity Documentation, publication page. docs.soliditylang.org
- “Ethereum: A Secure Decentralised Generalised Transaction Ledger (Yellow Paper),” Ethereum Foundation, technical reference. Ethereum GitHub
- “OpenZeppelin Contracts,” OpenZeppelin Docs, library documentation. OpenZeppelin Docs
- “Chainlink Documentation,” Chainlink, developer docs portal. Chainlink Documentation
- “OWASP Smart Contract Security Verification Standard,” OWASP, project page. OWASP Foundation
- “Smart contracts,” Law Commission (England and Wales), report page. Law Commission
- “Technical intro to Ethereum,” Ethereum.org, developer docs. ethereum.org
- “OpenZeppelin Contracts (GitHub),” OpenZeppelin, repository readme. GitHub
- “Blockchain Technology Overview (NIST IR 8202),” NIST, publication page and PDF. and https://nvlpubs.nist.gov/nistpubs/ir/2018/nist.ir.8202.pdf csrc.nist.gov